More than 600,000 small office/home office (SOHO) routers are estimated to have been bricked and taken offline following a destructive cyber attack staged by unidentified cyber actors, disrupting users’ access to the internet.
The mysterious event, which took place between October 25 and 27, 2023, and impacted a single internet service provider (ISP) in the U.S., has been codenamed Pumpkin Eclipse by the Lumen Technologies Black Lotus Labs team. It specifically affected three router models issued by the ISP: ActionTec T3200, ActionTec T3260, and Sagemcom.
“The incident took place over a 72-hour period between October 25-27, rendered the infected devices permanently inoperable, and required a hardware-based replacement,” the company said in a technical report.
The blackout is significant, not least because it led to the abrupt removal of 49% of all modems from the impacted ISP’s autonomous system number (ASN) during the time-frame.
While the name of the ISP was not disclosed, evidence points to it being Windstream, which suffered an outage around the same time, causing users to report a “steady red light” being displayed by the impacted modems.
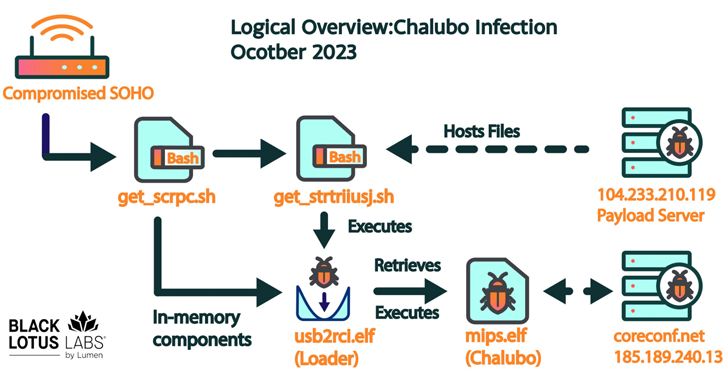
Now, months later, Lumen’s analysis has revealed a commodity remote access trojan (RAT) called Chalubo – a stealthy malware first documented by Sophos in October 2018 – as responsible for the sabotage, with the adversary opting for it presumably in an effort to complicate attribution efforts rather than use a custom toolkit.
“Chalubo has payloads designed for all major SOHO/IoT kernels, pre-built functionality to perform DDoS attacks, and can execute any Lua script sent to the bot,” the company said. “We suspect the Lua functionality was likely employed by the malicious actor to retrieve the destructive payload.”
That said, the exact initial access method used to breach the routers is currently unclear, although it’s theorized that it may have involved the abuse of weak credentials or exploited an exposed administrative interface.
Upon gaining a successful foothold, the infection chain proceeds to drop shell scripts that pave the way for a loader ultimately designed to retrieve and launch Chalubo from an external server. The destructive Lua script module fetched by the trojan is unknown.
A notable aspect of the campaign is its targeting of a single ASN, as opposed to others that have typically targeted a specific router model or common vulnerability, raising the possibility that it was deliberately targeted, although the motivations behind it are undetermined as yet.
“The event was unprecedented due to the number of units affected – no attack that we can recall has required the replacement of over 600,000 devices,” Lumen said. “In addition, this type of attack has only ever happened once before, with AcidRain used as a precursor to an active military invasion.”


So the attack happened in October 2023 but it was only revealed to the public now? Or is it that it was public back then but people didn’t pay attention?
Also the part where they say it has only ever happened as a precursor to a military invasion sort makes me think that this attack was some nation state practicing or signalling what they would do if they were in active cyber warfare which would be bad for the world if people in the competing nations didn’t have internet access, even if it was only for a day or two.
Anti Commercial-AI license (CC BY-NC-SA 4.0)
In the actual report linked in this article it says they were aware of the attack as it was happening and that they don’t believe it was a state actor
So the company was aware but I was wondering on whether it was public knowledge released today or it was released back then but no one paid attention.
Also the report says that they don’t believe it is a nation state actor because it doesn’t match with any known malicious clusters but it’s likely that countries have multiple unknown clusters they can test with if necessary.
Anti Commercial-AI license (CC BY-NC-SA 4.0)
these people would find out that there is such thing as fm radio. and that lot of their phones is capable of receiving it.
I was more thinking about all the services that rely on internet access to function. Like most economic systems would basically crash or grind to a halt.
There are a lot of products that don’t really need to be connected to the internet to do their job but are being connected anyways and would get bricked if access to the internet didn’t work. For example internet connected security cameras that don’t have cables connecting to where the data is being stored would be shot as well.
I mean the extent of the damage is really dependent on how the malware was spread which we don’t know yet so still mostly speculation on how damaging it could be.
Anti Commercial-AI license (CC BY-NC-SA 4.0)
we are talking about cheap home dsl routers here. i think that extent of the damage here is that someone has to revert to offline porn.
Mobile data plans exist… just saying 😁
Security cameras, or other security devices, including ATMs, or some alarm systems, sound compatible with attacking a single ASN: if the attacker knew the IP pool assigned to their target, and the possible modem/router model, targeting the ASN would guarantee taking down their actual target… plus some 600,000 “collateral damage” as a smoke screen.
It’s the end point modem+router. It’s like saying removing the landline phone from people’s house without destroy the exchange boxes would cripple communication. It’s not cause they are easily replaced.